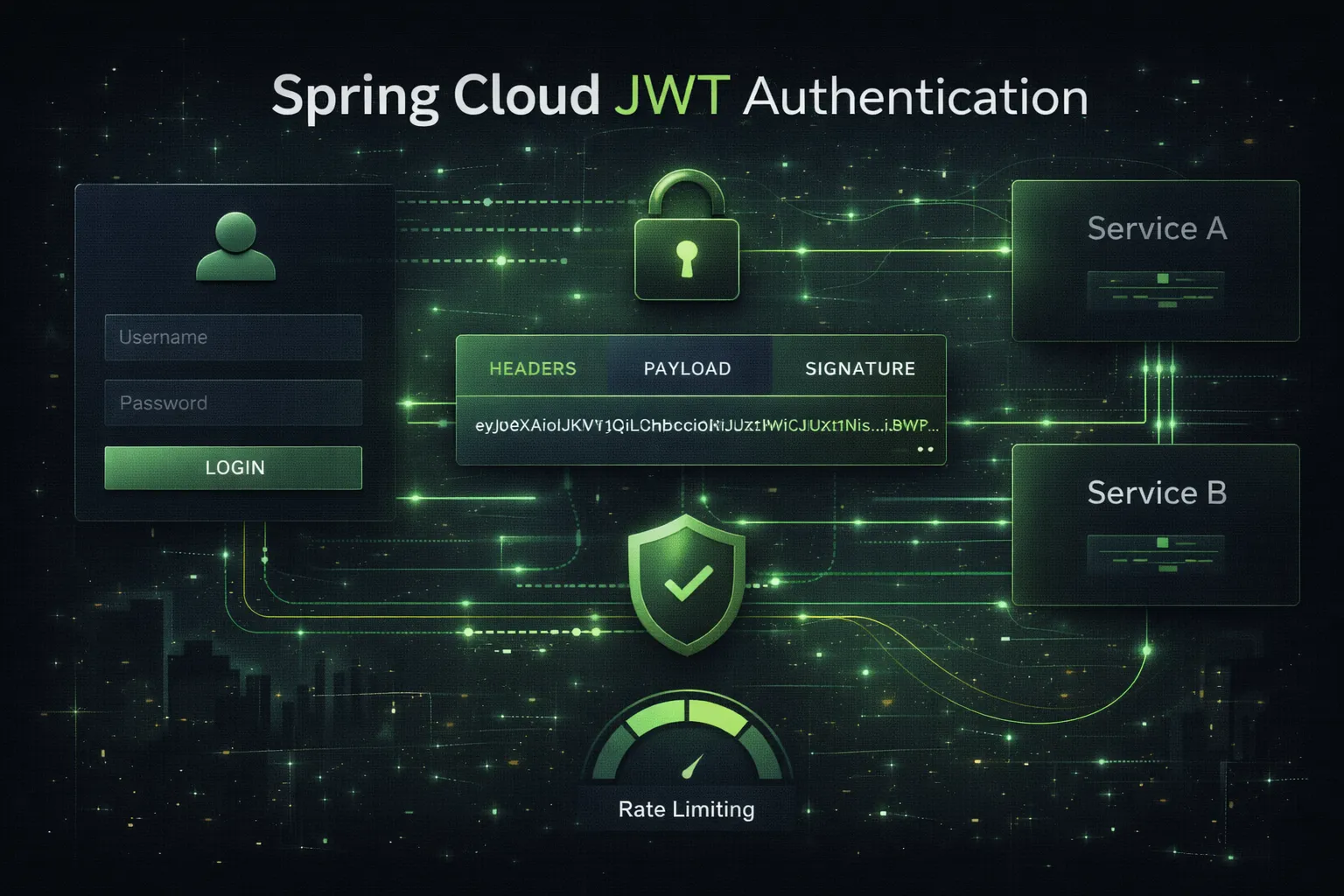
Spring Cloud JWT Authentication
Full-stack JWT authentication system with Spring Boot, Spring Cloud Config, Redis rate limiting, and a standalone Angular 20 frontend.
Technologies Used
Key Features
Overview
A full-stack authentication system built as a personal project to deepen my understanding of secure authentication patterns, Spring Cloud microservice configuration, distributed rate limiting, and modern Angular architecture.
The project combines a multi-module Spring Boot backend with a standalone Angular 20 frontend, focusing on clean separation of concerns across security, configuration, and UI layers.
What I Built
Backend (Spring Boot)
- Designed a multi-module Maven project with a dedicated Spring Cloud Config Server and a separate JWT authentication service, learning how to manage externalized configuration across microservices.
- Implemented cookie-based JWT authentication using HttpOnly secure cookies instead of localStorage, gaining hands-on experience with XSS mitigation strategies and secure token lifecycle management (access tokens, refresh tokens, logout).
- Built a CSRF protection layer using Spring Security’s filter chain, understanding the interaction between cookie-based auth and cross-site request forgery prevention.
- Developed a distributed rate limiting filter using Redis and Bucket4j, applying per-IP throttling on authentication endpoints to prevent brute-force attacks.
- Implemented RFC 7807 Problem Details for structured error responses on conflict and validation errors.
Frontend (Angular 20)
- Built a standalone Angular application using
bootstrapApplicationand lazy-loaded routes, learning the modern Angular standalone architecture without NgModules. - Created reactive forms with custom validators for password strength, email format, and field constraints.
- Implemented a global HTTP interceptor that handles credential forwarding, automatic token refresh on 401 responses, and redirect-to-login on session expiry.
- Built UI-level error handling that reads
Retry-Afterheaders for rate limit feedback and parses Problem Detail responses for backend validation messages.
Skills and Technologies Practiced
- Spring Security filter chain configuration and custom security filters
- JWT token generation, validation, and cookie-based session management
- Spring Cloud Config for centralized, environment-specific configuration
- Redis integration for distributed state (rate limit buckets)
- Angular standalone architecture, reactive forms, and HTTP interceptors
- Cross-cutting concerns: CSRF, rate limiting, error standardization
Outcome
This project gave me a solid, end-to-end understanding of how authentication, authorization, and security hardening work together across backend and frontend. It serves as a reference implementation I can build on for future projects requiring secure user authentication.